What Are CUI and FCI?
Organizations that work with the federal government often encounter two critical data categories: Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). While both are unclassified, they require protection under federal cybersecurity requirements — particularly for companies within the Defense Industrial Base (DIB).
Understanding the distinction between CUI and FCI is essential for compliance, risk management, and successful participation in federal contracting.
What Is Controlled Unclassified Information (CUI)?
Controlled Unclassified Information (CUI) is unclassified information that requires safeguarding or dissemination controls under federal law, regulation, or government-wide policy.
Although not classified, CUI is sensitive. If improperly disclosed, altered, or destroyed, it could impact national security, privacy, economic interests, or government operations.
CUI spans a wide range of information categories, including:
- Personally Identifiable Information (PII)
- Financial and proprietary data
- Export-controlled technical data (ITAR/EAR)
- Controlled technical information (CTI)
- Protected health information (PHI)
- Law enforcement sensitive information
CUI protection requirements are primarily defined in NIST SP 800-171 and enforced contractually through DFARS 252.204-7012 and related clauses.
What Is Federal Contract Information (FCI)?
Federal Contract Information (FCI) is unclassified information provided by or generated for the government under a federal contract that is not intended for public release.
In simpler terms, FCI is information created or received while performing a federal contract.
Examples of FCI include:
- Contract performance reports
- Internal emails discussing contract deliverables
- Technical specifications provided in a contract
- Non-public contract pricing or schedules
- Work instructions tied to contract performance
FCI does not include publicly releasable information.
While FCI is generally less sensitive than CUI, it still requires protection. FCI safeguarding requirements are outlined in FAR 52.204-21, which establishes basic cybersecurity controls for federal contractors.
Why CUI and FCI Matter
Both CUI and FCI carry legal and contractual protection requirements. The difference lies in the level of impact if compromised.
National Security
- CUI often includes technical or operational data that could harm national defense or critical infrastructure if exposed.
- FCI may reveal sensitive aspects of government operations or acquisition strategies.
Privacy and Identity Protection
- CUI frequently includes PII and other sensitive personal data.
- FCI may contain personnel or subcontractor information tied to contract execution.
Economic and Competitive Impact
- CUI may include intellectual property, export-controlled data, or trade secrets.
- FCI can expose pricing strategies, proprietary approaches, or contract structures.
Compliance and Contract Eligibility
Failure to properly safeguard CUI or FCI can result in:
- Contract termination
- Loss of future award eligibility
- False Claims Act exposure
- Reputational damage
- Suspension or debarment
For defense contractors, these risks are business-critical.
Types of CUI vs. FCI
Understanding what falls into each category is essential.
Examples of CUI
- Export-controlled drawings and technical data
- Controlled Technical Information (CTI)
- HIPAA-regulated health information
- Sensitive law enforcement information
- Privacy Act–protected data
CUI must be clearly identified, marked, and protected according to federal standards.
Examples of FCI
- Non-public contract deliverables
- Statements of Work (SOWs)
- Government-provided performance data
- Internal communications about contract performance
- Acquisition-sensitive but unclassified information
FCI does not require formal CUI marking but must still be protected from unauthorized access.
Identifying CUI and FCI in Your Organization
Many contractors struggle not with protection — but with identification.
Organizations should:
1. Review Contract Clauses
Examine FAR and DFARS clauses in your contracts.
- FAR 52.204-21 indicates FCI handling requirements.
- DFARS 252.204-7012 signals CUI handling obligations.
2. Conduct Data Classification Assessments
Map data flows across systems. Identify:
- Where contract information is stored
- Whether any information qualifies as CUI
- Who has access to it
3. Engage Legal and Compliance Experts
Misidentifying CUI as FCI — or vice versa — can result in compliance gaps.
4. Document System Boundaries
Determine which systems process FCI only and which process CUI. This distinction affects your required cybersecurity controls.
How to Mark and Handle CUI
CUI requires formal marking and handling procedures.
Organizations should:
- Apply clear “Controlled Unclassified Information” or “CUI” banners
- Include category markings when applicable
- Add dissemination controls where required
- Use approved storage and transmission methods
- Train employees on proper handling and reporting procedures
Proper marking ensures downstream recipients understand their protection obligations.
How to Safeguard FCI
While FCI does not require formal CUI markings, it must be protected with basic cybersecurity safeguards under FAR 52.204-21.
At minimum, organizations must implement controls such as:
- Limiting system access to authorized users
- Verifying user identity
- Controlling physical access
- Protecting information during transmission
- Monitoring and controlling system access
These foundational safeguards are often referred to as “Level 1” protections under CMMC.
FCI vs. CUI: Key Differences
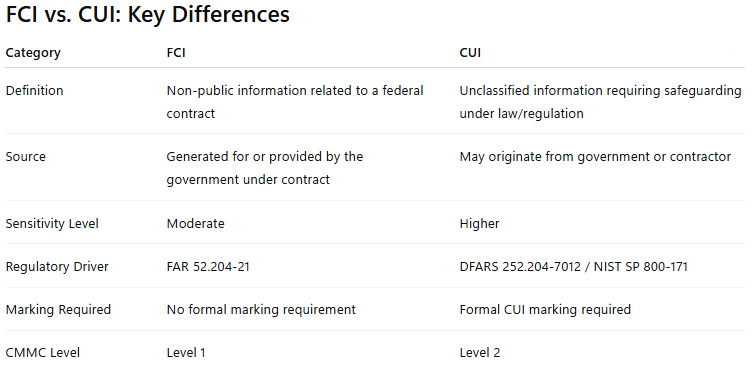
In short:
- All CUI in a contract environment is sensitive.
- Most contractors handle FCI.
- Not all contractors handle CUI.
Understanding which applies to you determines your compliance path.
CMMC, FCI, and CUI
The Cybersecurity Maturity Model Certification (CMMC) formalizes protection requirements for defense contractors.
- CMMC Level 1 applies to organizations handling FCI only.
- CMMC Level 2 applies to organizations handling CUI.
If your environment processes CUI, you must implement the 110 security requirements of NIST SP 800-171 and undergo third-party assessment (unless eligible for self-assessment under specific criteria).
If you handle only FCI, you must implement the 15 basic safeguarding requirements of FAR 52.204-21.
Misunderstanding this distinction can lead to over-engineering — or worse, under-protecting sensitive data.
Safeguarding Government Information: A Business Imperative
Whether your organization handles FCI, CUI, or both, safeguarding federal information is not optional.
By:
- Accurately identifying data types
- Implementing appropriate safeguards
- Training employees
- Monitoring compliance
- Aligning with CMMC requirements
You reduce risk, maintain eligibility for federal contracts, and demonstrate maturity as a trusted defense partner.
Understanding the difference between FCI and CUI is the first step. Implementing the right protections is what keeps you in the game.