SecureiTSM provides structurcd assessment support for organizations navigating official CMMC Level2 audits. Our model aligns directly with the CMMC Assessment Process (CAP), supporting both pre-assessment readiness and full implementation evaluation. We assis! Wit evidenCe cooMination, aSSessarinieraciion, and audit eXecution WINouT Compromising C3PAD independence. The resullis acontrolled. predictable, and defensible assessment expetience buil for DoD contractors.




SecureITSM provides an integrated security and compliance operating model designed for DoD contractors navigating CMMC Level 2 assessments and ongoing regulatory oversight.
Stage 1 is a C3PAO-led readiness review that validates documentation completeness, scope accuracy, and evidence availability prior to a full audit. No controls are scored during this stage. The outcome is a formal readiness determination that authorizes progression to Stage 2.
The C3PAO documents one of two outcomes:
• Ready to Proceed to Stage 2
• Not Ready, corrective action required
No scoring or certification determination occurs at this stage.
The C3PAO reviews the SSP to confirm it accurately reflects the in-scope environment, boundary definitions, and control implementation intent. The SSP must logically map each requirement to operational reality and align with NIST SP 800-171 structure and expectations.
Assessors verify that required documentation artifacts exist and are accessible. Each control must be supported by traceable, current, and properly versioned evidence aligned to NIST SP 800-171A assessment objectives.
Stage 1 confirms whether controls are clearly categorized as Common, Hybrid, or System-Specific. Inherited controls must be distinguishable from customer-owned controls, and implementation delimiters must be explicit.
The assessment boundary is validated to ensure that the documented scope matches actual infrastructure, services, and data flows. Scope drift or undocumented systems can halt progression to Stage 2.

SecureITSM does not perform a pre-assessment. Instead, readiness is engineered through our Control Manager platform, which replicates DoD eMASS control inheritance principles and enforces documentation integrity continuously.
Common Control Provider logic enables controls, status, artifacts, and implementation statements to propagate automatically to receiving systems. This eliminates redundant documentation and preserves audit defensibility.
Inherited controls automatically carry compliance status, artifact history, timestamps, and test references. Risk transfer is documented if a provider control becomes non-compliant.
Before Stage 1 begins, inheritance is frozen, evidence is locked, and MSP-level operational changes are suspended. This ensures documentation integrity during C3PAO review.

Stage 2 is the official CMMC Level 2 audit phase. The C3PAO evaluates the actual implementation and operational effectiveness of security requirements using NIST SP 800-171A assessment methods. This stage results in formal control-level determinations.
The assessment begins with a formal in-brief meeting to confirm scope, logistics, control coverage, and evaluation approach. Documentation access and personnel availability are validated before testing begins.
Assessors review policies, procedures, SSP content, configurations, and logs to verify documentation accuracy and completeness. Evidence must align directly to assessment objectives.
Key stakeholders are interviewed to confirm operational understanding, control ownership, and process execution. Responses must match documented implementation.
Assessors perform technical validation of configurations, logging behavior, access controls, encryption settings, and system safeguards to verify control operation.
During the assessment window, assessors may request additional artifacts or clarification. All responses must remain controlled, accurate, and aligned to documented scope.
Each control receives a Met or Not Met determination. Final reporting and certification decisions are issued by the C3PAO. SecureITSM does not influence scoring or outcomes.

SecureITSM provides structured execution support while maintaining strict separation from scoring authority.
Artifacts are presented through the Control Manager platform in a structured, traceable format. Version history and inheritance lineage remain visible to the assessor.
SecureITSM coordinates clarification requests, manages logistics, and prevents scope drift while ensuring technical answers remain accurate and controlled.
This preserves assessment integrity.
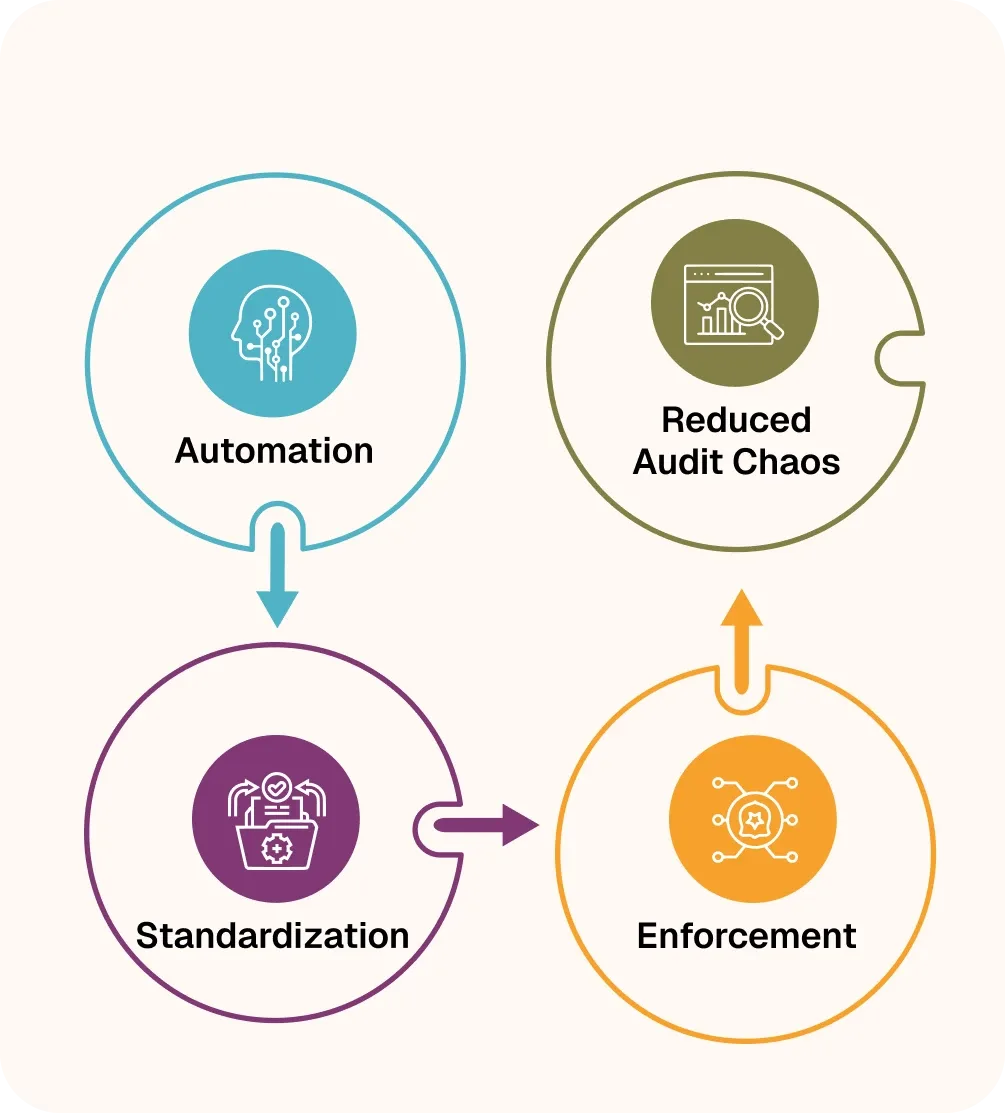
Key to our model is our application, audit automation, and hands-on guidance throughout the audit process. SecureITSM replaces ad-hoc consulting with standardized workflows, automation, and an enforcement-driven operating model.

Evidence handling, tracking, and coordination are system-driven not spreadsheet-based.

Every assessment follows the same repeatable process reducing variance and confusion.

Controls, evidence, and operations are governed through a centralized enforcement engine.
SecureITSM delivers structured, audit-aligned CMMC assessment support covering evidence, assessor interaction, and post-assessment continuity. Defined by methodical, standards driven execution without shortcuts or assurances.
