When Controlled Unclassified Information (CUI) moves into contractor operated systems, civilian agencies increasingly expect structured NIST 800-171 compliance. Contract clauses may differ, but the safeguarding outcome is consistent. SecureITSM helps federal contractors implement defensible controls, document evidence, and align with evolving federal CUI requirements across DHS, GSA, and GWAC task orders.
Civilian agency cybersecurity expectations are converging around consistent protection of Controlled Unclassified Information (CUI). While clause language may differ across agencies, safeguarding outcomes increasingly align with NIST SP 800-171 controls. The progression of the FAR CUI rule further standardizes federal CUI requirements, reducing variability across civilian contracts and task orders.
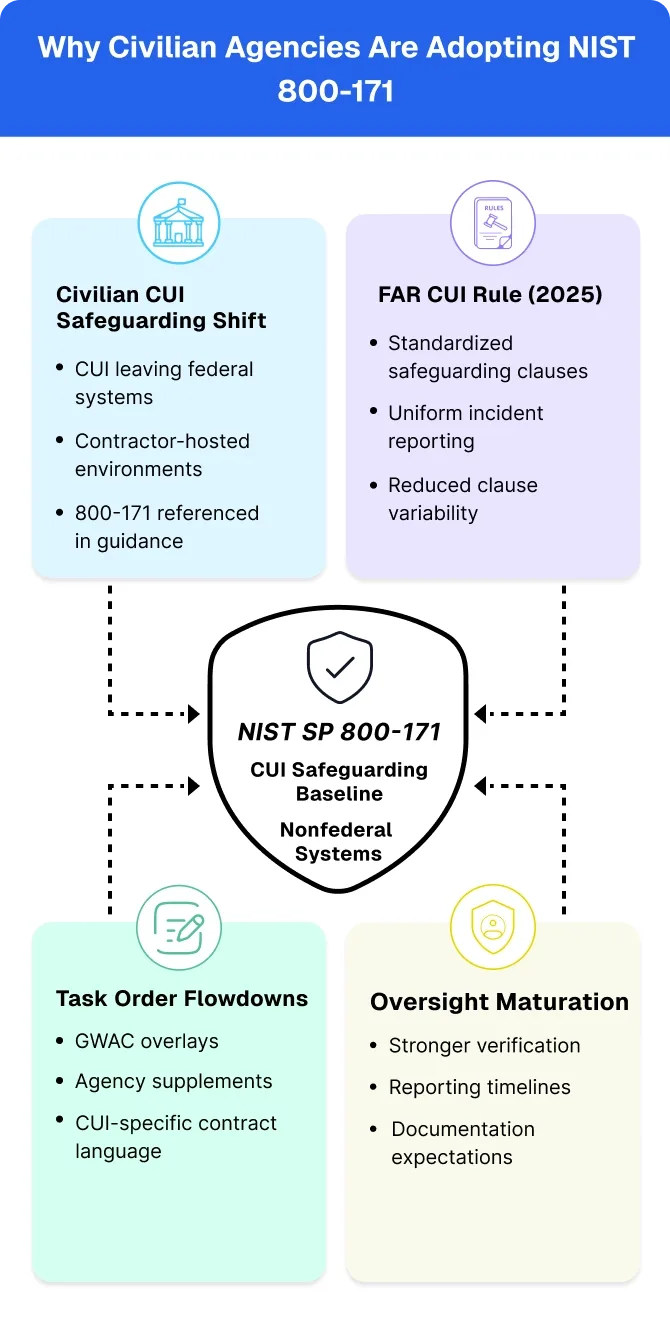
Civilian agencies increasingly reference NIST 800-171 when CUI resides in contractor-operated systems, even when the framework is not explicitly cited. GSA guidance, agency manuals, and task-order clauses frequently flow down safeguarding expectations that mirror 800-171 requirements. Clause language may vary, but the operational expectation remains consistent: contractors hosting CUI must implement structured, documented, and auditable security controls.
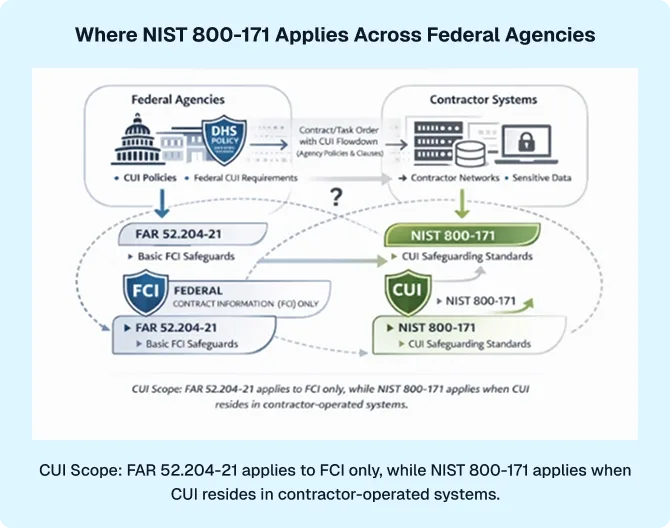
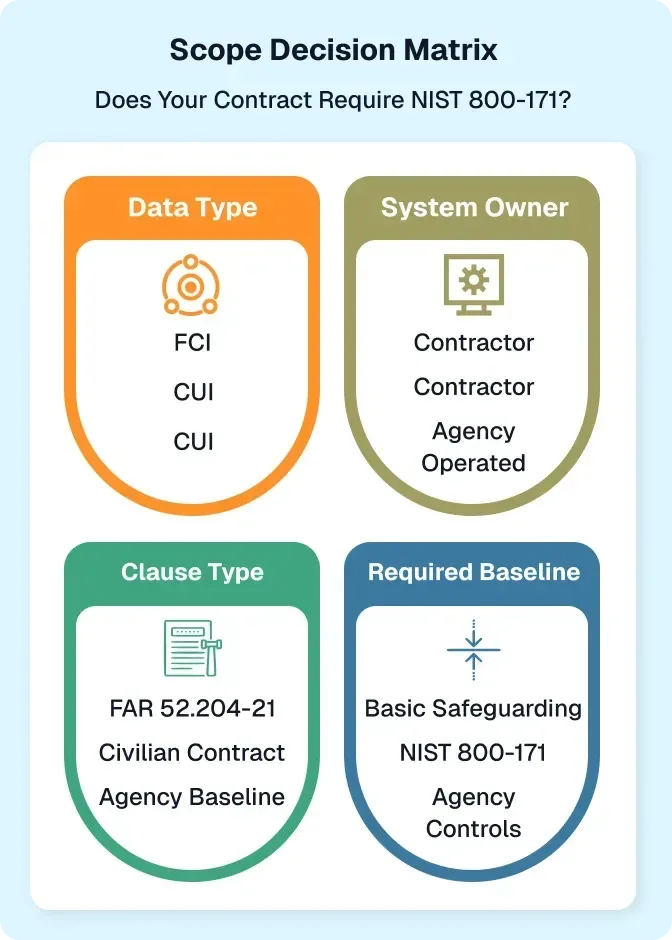
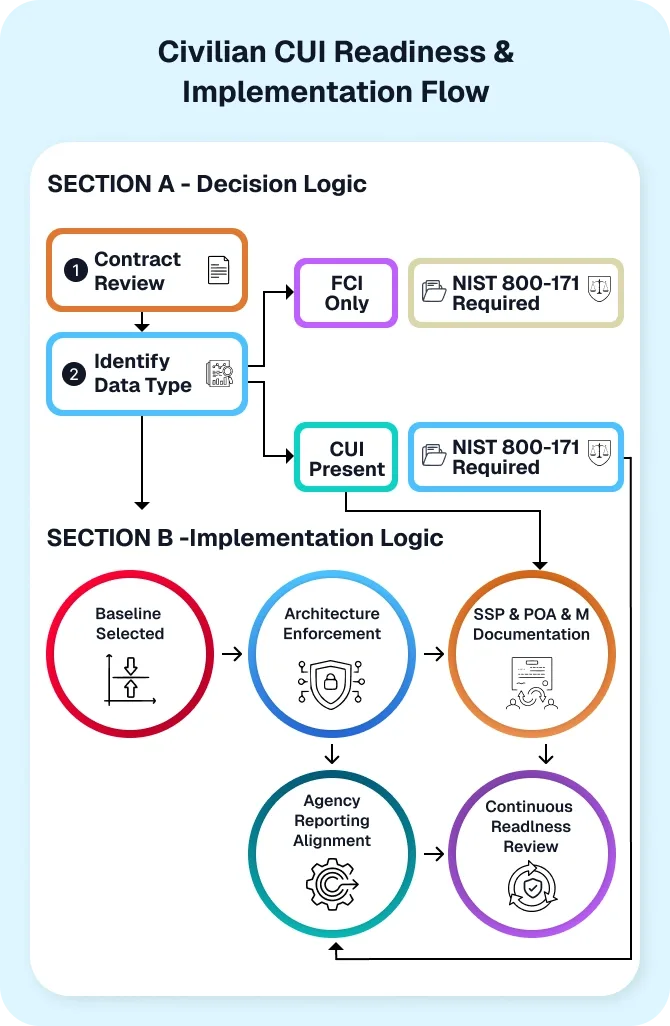
FAR 52.204-21 establishes basic safeguarding requirements for Federal Contract Information (FCI). It does not establish a comprehensive control baseline for CUI. As civilian agencies increasingly differentiate FCI from CUI in contracts, NIST SP 800-171 becomes the practical baseline for protecting CUI in nonfederal systems.
The FAR CUI rule introduces standardized safeguarding and incident reporting language across executive agencies. The FAR CUI proposed rule signals a government-wide effort to harmonize federal CUI requirements. Once finalized, contractors can expect more uniform application of 800-171-style controls across civilian contracts, reducing clause-by-clause interpretation risk.
Although civilian agencies historically lacked centralized scoring models, oversight mechanisms are evolving. Agencies are strengthening reporting timelines, documentation expectations, and compliance verification practices. This shift places greater emphasis on demonstrable control implementation, not policy declarations.
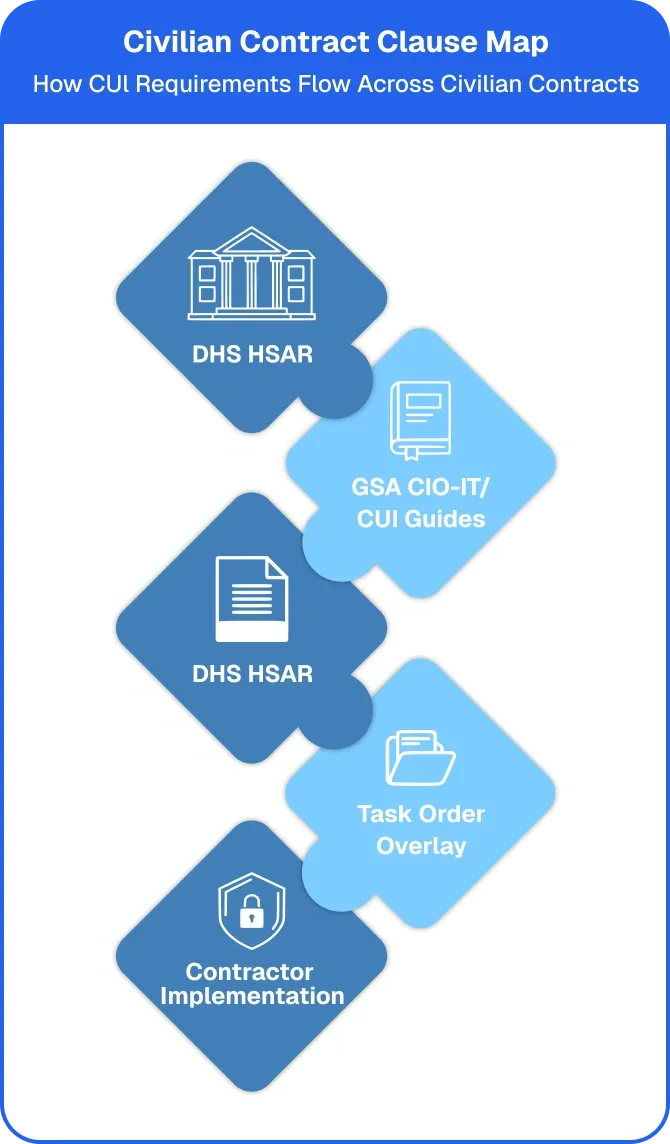
Government-wide acquisition contracts (GWACs) often establish baseline cybersecurity language, but CUI-specific obligations frequently appear at the task-order level. Contractors must analyze each order individually to determine safeguarding requirements, making structured CUI scope determination essential.
Agencies such as DHS apply safeguarding expectations through agency supplements and reporting mandates. While the clause may not explicitly cite NIST 800-171, the security outcome often aligns with its control structure. Understanding how to map agency-specific language to 800-171 safeguards reduces implementation gaps.
The publication of NIST SP 800-171 Rev. 3 reinforces the federal government’s commitment to evolving CUI protection standards. Civilian agencies will progressively align policy language and task-order references to Rev. 3, requiring contractors to maintain forward-looking compliance posture.
Organizations that proactively implement NIST 800-171 controls are positioned to absorb future clause updates with minimal disruption. Standardization across civilian agency cybersecurity environments reduces remediation cost, audit friction, and contract execution risk.

The distinction between Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) determines the safeguarding baseline. FAR 52.204-21 establishes basic controls for FCI. It does not establish the full control structure required for CUI. When CUI resides in contractor-operated systems, NIST SP 800-171 becomes the governing security framework.
Misapplying FAR basic safeguarding to CUI creates compliance exposure.
Civilian contracts trigger NIST 800-171 when CUI leaves federal systems and resides in contractor-operated environments. The specific clause may vary, but the safeguarding expectation aligns with 800-171 controls. Contract analysis must consider agency supplements, task orders, and DHS safeguarding requirements
DHS safeguarding requirements may not always cite NIST 800-171 directly, but their "adequate security" language maps closely to structured control implementation. Contractors supporting DHS programs must analyze HAR provisions alongside federal CUI requirements to determine baseline controls.



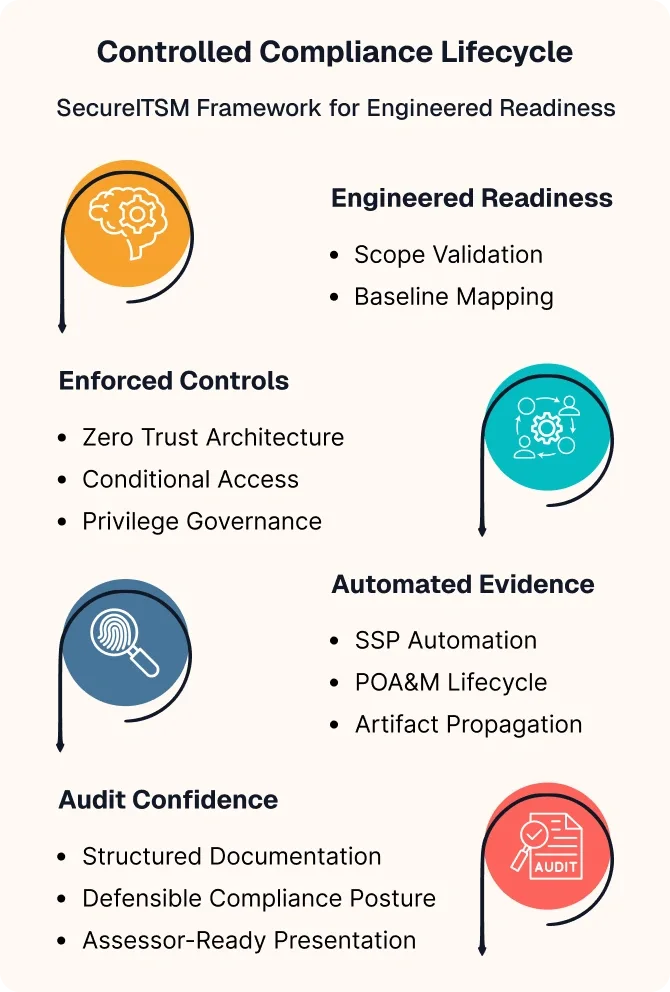
SecureITSM provides NIST 800-171 consulting grounded in operational ISSO experience across civilian agency cybersecurity environments. We perform structured scope validation, control gap analysis, and remediation engineering aligned to contract language. Rather than generic advisory, we engineer control implementation pathways that map directly to documented compliance objectives.
Effective NIST 800-171 compliance extends beyond documentation, it requires enforceable architecture. SecureITSM designs and deploys Zero Trust aligned environments, including Microsoft GCC & GCC High cloud strategies, identity governance, and conditional access enforcement.
The same secure foundation that supports civilian contracts also aligns with DFARS and CMMC requirements, ensuring architectural continuity across federal engagements.
Civilian contracts increasingly require demonstrable control implementation. SecureITSM operationalizes NIST 800-171 SSP and POA&M management through structured evidence mapping and documentation governance.
Our Control Manager platform models inheritance logic, artifact propagation, and audit-ready presentation reducing spreadsheet dependency and manual documentation risk.


DHS safeguarding requirements are implemented through HSAR 3052.204-72 and associated agency policies. Rather than directly citing NIST 800-171, DHS defines "adequate security" through compliance with current DHS directives and structured reporting mandates.
DHS incident reporting requirements introduce defined timelines, reporting portals, and documentation expectations that extend beyond baseline safeguarding controls.
The practical result: contractors must map 800-171 controls to DHS safeguarding language to ensure compliance alignment.
GSA CUI requirements often appear through CIO-IT security guides, CUI program documentation, and task order level clauses While master GWAC vehicles establish baseline cybersecurity expectations, CUI specific safeguarding frequently flows through the ordering agency.
Alliant, Polaris, and similar vehicles may incorporate agency overlays that trigger NIST 800-171-aligned implementation withi contractor-operated systems.
Structured contract review ensures proper baseline determination.
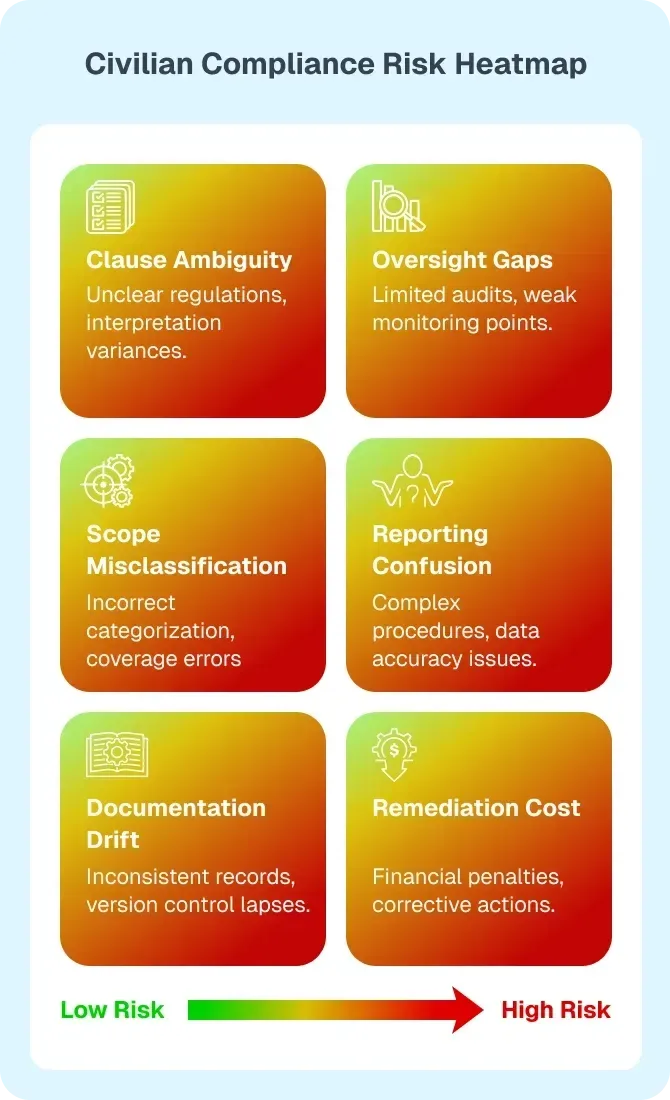
Civilian federal contractor compliance is shaped by clause variability, evolving federal CUI requirements, and uneven oversight mechanisms. Without structured interpretation and implementation, contractors face scop misalignment, documentation gaps, and elevated audit risk.

Civilian solicitations often mix legacy contract language, policy references, and safeguarding terminology without clearly defining the control baseline. This ambiguity increases the risk of applying inconsistent controls across contracts.

Unlike centralized scoring environments, civilian agency cybersecurity oversight may vary significantly by agency and contract type. Federal contractor compliance therefore depends on internal control maturity rather than reliance on external validation.

Misclassifying contract data leads to structural safeguarding gaps. Applying FAR 52.204-21 controls to CUI instead of NIST 800- 171 creates exposure. Clear scope determination is essential for defensible implementation.

GWAC master vehicles establish baseline posture, but CUI obligations frequently appear at the task-order level. Each order must be analyzed independently to prevent inconsistent security implementation.
Spreadsheet-driven compliance management introduces artifact inconsistencies and undocumented changes. Federal contractor cybersecurity maturity requires structured evidence governance.
Civilian agency cybersecurity obligations require structured scope determination and disciplined implementation. Federal contractors must proactively identity CUI i n contracts, determine the correct safeguarding baseline, and operationalize documentation governance. NIST 800-171 is required when CUI resides in contractor-operated nonfederal systems and contractors must be able to demonstrate it.
Early contract review prevents implementation errors. Contractors must analyze solicitation language, attachments, and data flow to determine whether Controlled Unclassified Information will reside in their environment. Understanding how to identify CUI in contracts ensures proper baseline selection before system architecture decisions are made.
If only Federal Contract Information (FCI) is present, FAR 52.204-21 basic safeguarding may apply. If CUI is present in contractor-operated systems, NIST SP 800-171 becomes the required baseline. Clear differentiation prevents over-implementation or regulatory exposure.
Prime contractors must review CUI flowdown requirements in subcontracts and task orders. Safeguarding obligations extend beyond the prime entity when CUI is shared across operational partners. Structured clause analysis ensures consistent control application across the contract chain.
NIST 800-171 compliance requires more than policy statements. Contractors must implement enforceable controls, structure SSP documentation, and POA&M lifecycle management. Evidence automation reduces manual documentation drift and strengthens defensibility.
Agency overlays, including DHS incident reporting requirements, introduce additional procedural obligations. Contractors must align reporting workflows and internal governance to agency timelines. Regular readiness validation ensures ongoing compliance stability.
SecureITSM’s compliance engineering model supports federal contractors operating under complex cybersecurity obligations. While civilian agency clauses may vary, the underlying safeguarding architecture, Zero Trust enforcement, and documentation governance remain consistent. Real contractor outcomes demonstrate the impact of engineered readiness and automated evidence management.
Partnering with SecureITSM has completely transformed our IT operations. The AgileDefend™ platform provides unmatched visibility, intelligent automation, and precise control across our GCC High environment. We’ve significantly reduced manual compliance tasks while improving incident response speed and operational reliability. SecureITSM’s technical depth, proactive approach, and ongoing monthly reviews ensure that our systems remain secure, compliant, and mission-ready at all times.
Our integrated security platform provides end-to-end protection, monitoring, and incident response capabilities to keep your business safe from evolving cyber threats.
NIST SP 800-171 applies when Controlled Unclassified Information (CUI) resides in contractor-operated nonfederal systems. If a civilian contract involves CUI stored, processed, or transmitted within your environment, federal contract CUI compliance requires implementation of 800-171 controls unless an agency mandates a different baseline. If only Federal Contract Information (FCI) is present, FAR 52.204-21 basic safeguarding may apply instead.
Civilian agency clauses vary, safeguarding expectations do not. If your contract involves CUI, NIST 800-171 may already apply. SecureITSM provides structured compliance engineering, Zero Trust enforcement, and documentation governance aligned to federal contract CUI compliance requirements. Gain clarity before deployment. Reduce remediation risk before audit exposure.
